Scam Investigation Insight Portal Scam Phone Number Lookup Revealing Caller Identification
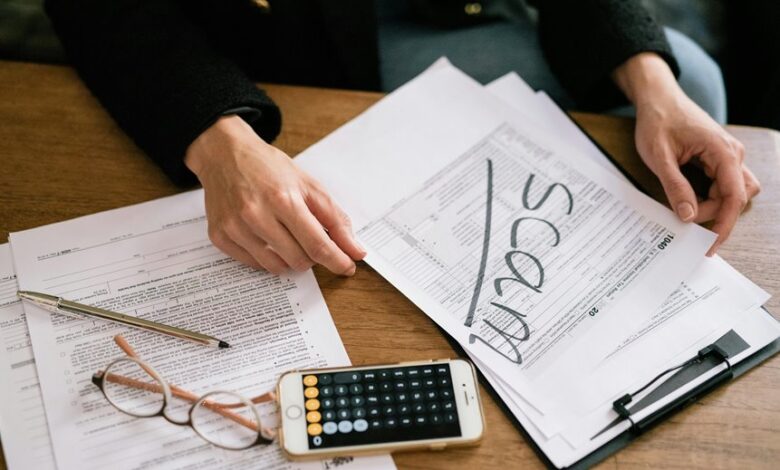
The Scam Investigation Insight Portal’s phone-number lookup offers traceable caller identification through documented data, timestamps, and cross-source verification. It highlights patterns linked to fraud networks while preserving user privacy. The approach emphasizes accountability, independent tool reliance, and evolving confidence scores as evidence accumulates. Vigilant assessment remains essential for safe engagement. This framework invites scrutiny of how evidence is gathered and weighted, leaving readers curious about the next steps and ongoing improvements.
What the Scam Phone Number Lookup Reveals
What does a Scam Phone Number Lookup reveal? The process highlights patterns in scam nuances, linking numbers to known fraud networks and suspicious behavior. It draws on robust caller databases, documenting reports, timestamps, and escalation notes. Findings emphasize transparency, traceability, and risk indicators, enabling informed decisions. Observers maintain vigilance, distinguishing legitimate contacts from dubious outreach while empowering freedom through accountability.
How to Verify Caller Identification Effectively
To verify caller identification effectively, researchers recommend a structured, evidence-based approach that weighs multiple data signals rather than relying on a single source. The method emphasizes cross-checking metadata, call patterns, and user reports while maintaining privacy. Practitioners document findings, compare sources, and update confidence scores. This disciplined practice supports how to verify caller identification with transparency, resilience, and accountability for a freedom-minded audience.
What to Do When You Identify a Suspicious Number
When a number is flagged as suspicious, immediate, methodical steps help minimize risk and preserve privacy.
The guide outlines What to do: document the caller, avoid sharing personal data, and suspend engagement until verification.
For Suspicious numbers, how to verify relies on independent sources and official lookup tools.
Caller identification should be cross-checked with trusted databases to confirm legitimacy.
Maximizing Safety: Best Practices and Privacy Considerations
Maximizing Safety: Best Practices and Privacy Considerations builds on the prior guidance for handling suspicious numbers by outlining concrete, research-backed steps to protect personal information while using caller identification tools.
The approach emphasizes scam awareness, careful data sharing, and regular caller ID verification to reduce exposure.
Users adopt privacy-conscious habits, verify sources, and limit permissions while maintaining vigilant, freedom-friendly, evidence-based safeguards.
Conclusion
In a coincidence of timing, the Scam Investigation Insight Portal arrives as a timely compass, aligning disparate signals into a coherent picture. The lookup reveals caller identification backed by timestamps, notes, and cross-source verification, while updating confidence with new evidence. This vigilant, evidence-based tool supports prudent decisions, preserving privacy even as risk indicators rise. By tracking patterns and anomaly clusters, readers glimpse a landscape where accountability and resilience guide safer, informed engagement with potentially suspicious numbers.
